SSO in DX Cloud
The instructions on this page focus primarily on the required steps to integrate into our Identity Platform (IdP) based on Keycloak, which gives you access to our DX Cloud Service via SSO.
| Please note that we offer this IdP Integration to access our DX Cloud Service via SSO. If you have your own IdP, we recommended to use it on SSO module to access and secure the Magnolia AdminCentral. In that case, you must configure the IdP settings on your own. |
Overview
The Magnolia SSO (single sign-on) module delegates authentication from a Magnolia instance to an OpenID Connect identity and access management application. The current iteration of the module has been successfully tested with open source Keycloak and cloud identity management software Okta, but all providers that follow the protocol should also be supported.
As Magnolia is already capable of full-fledged security, the intent is to only replace the authentication mechanism. A user on a third-party system with roles and groups is mapped to the equivalent Magnolia user roles and groups.
Keycloak settings for SSO
To integrate an external IdP Directory Service for Single-Sign-On (SSO) with DX Cloud, it’s possible to setup a connection via SAML or OpenID Connect (OIDC).
- Example: Azure AD Integration with Keycloak via OpenID Connect (OIDC)
-
As OIDC is the preferred way, the following instructions explain the basic Integration steps for Keycloak and Azure AD via OIDC authentication (OAuth2 for authorization). To integrate an existing Azure AD with Keycloak via OIDC, the following steps are required to be performed (ordered). All
AzureActions are performed via Microsoft Azure portal.
An Azure AD Premium P1/P2 subscription is required to map AppRoles to Users/Groups in Azure later.
|
Basic setup
|
To integrate your Azure AD with Keycloak using OIDC, we’ll need the following information to be securely(!) shared with Magnolia:
|
-
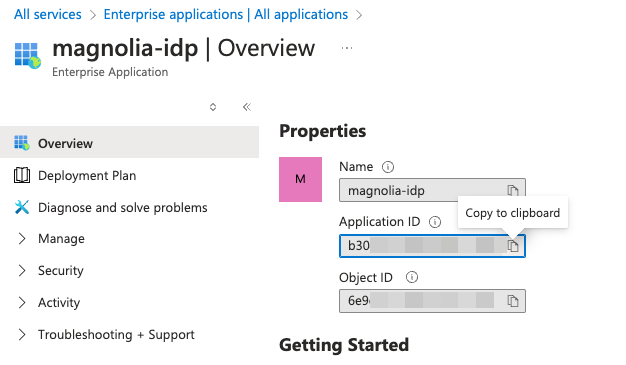
Create an Enterprise Application and copy the
ApplicationID(ie.1978A428-FY151-444B-AA32-GB18DCB7F482)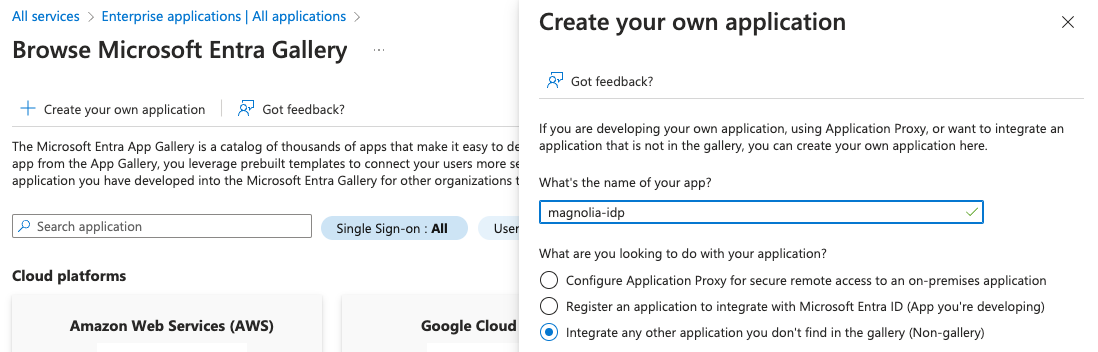
-
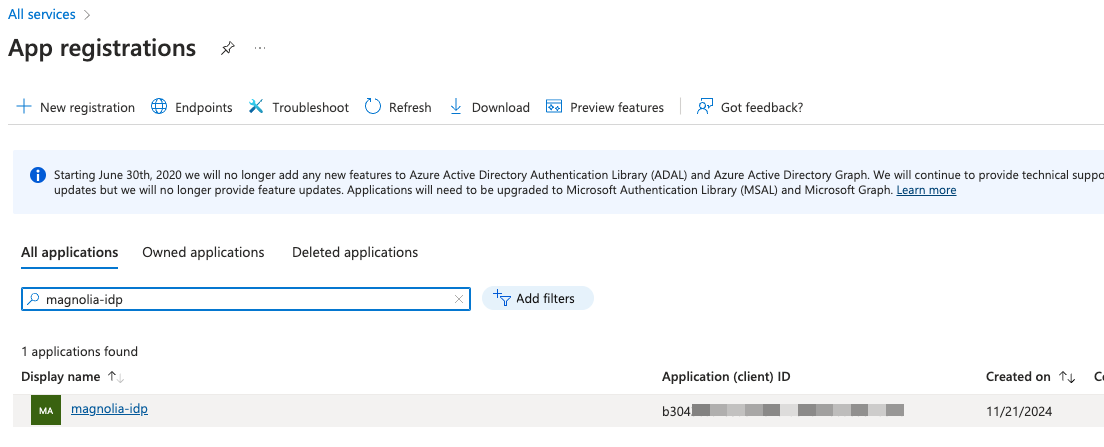
Navigate to App Registrations and find your recently created application and open it.
-
In Manage > Certificates & Secrets, create a
Client Secretand copy down the newSecret Value(Secret IDis not required).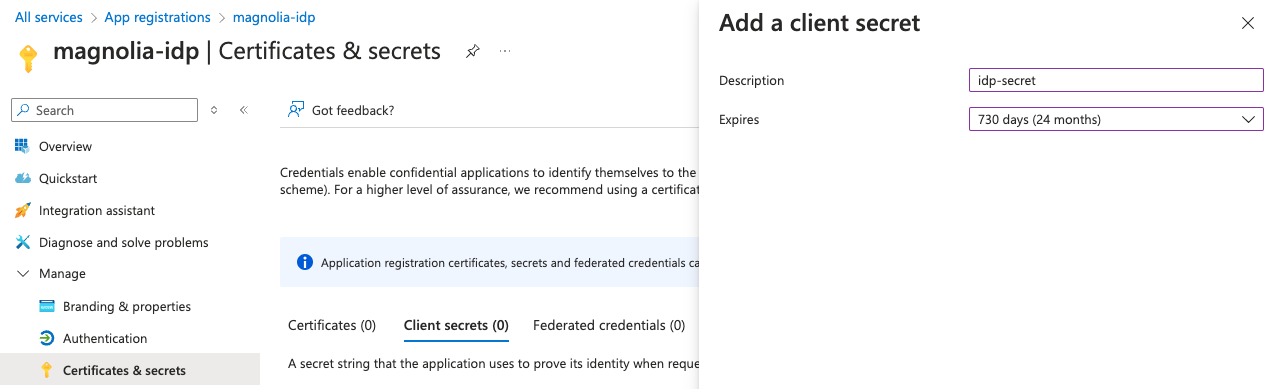

-
In App Registrations on the newly created app, open Overview > Endpoints and note the OpenID Metadata Document URL of the new Application.
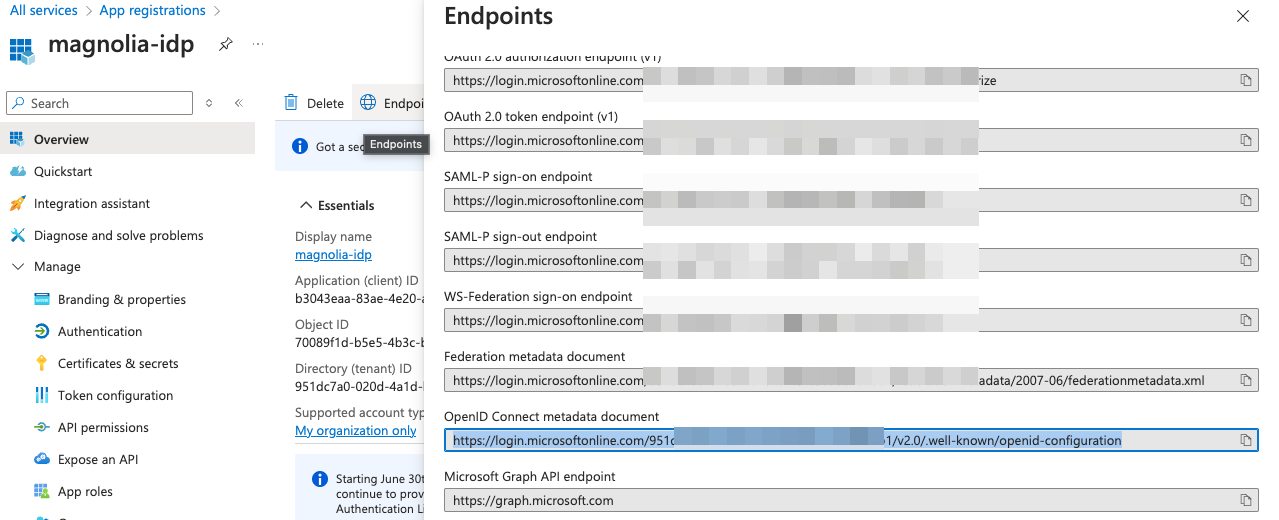
.well-knownMetadata document is publicly available and typically follows this formathttps://login.microsoftonline.com/<app-uuid>/v2.0/.well-known/openid-configuration. -
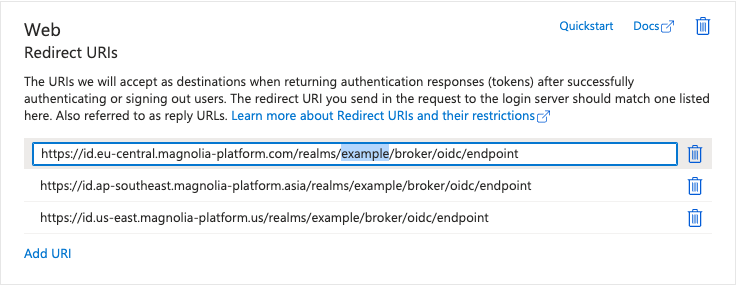
Finally, in the Authentication section of the App Registration, add the Magnolia Keycloak URLs as
valid redirect URIs(PlatformWeb). Please enter them in the following format (replace<customer>with your customer shortname):-
EMEA:
https://id.eu-central.magnolia-platform.com/realms/<customer>/broker/oidc/endpoint -
APAC:
https://id.ap-southeast.magnolia-platform.asia/realms/<customer>/broker/oidc/endpoint -
US:
https://id.us-east.magnolia-platform.us/realms/<customer>/broker/oidc/endpointAzure does not allow wildcards(*) in RedirectURIs, so you need to add each URL separately with the full path.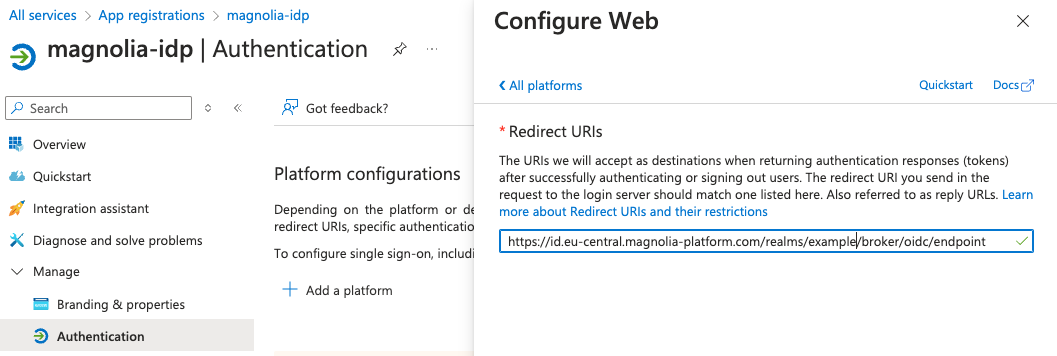
-
-
In the
<customer>realm under Identity Providers, create a new IdP Integration using the information received before.-
Client ID(Application ID) -
Client Secret(Application SecretSecret Value) -
Well-Known URL(OpenID Metadata Document URL including all necessary information)Fetch OIDC metadata to "autofill" basic Information
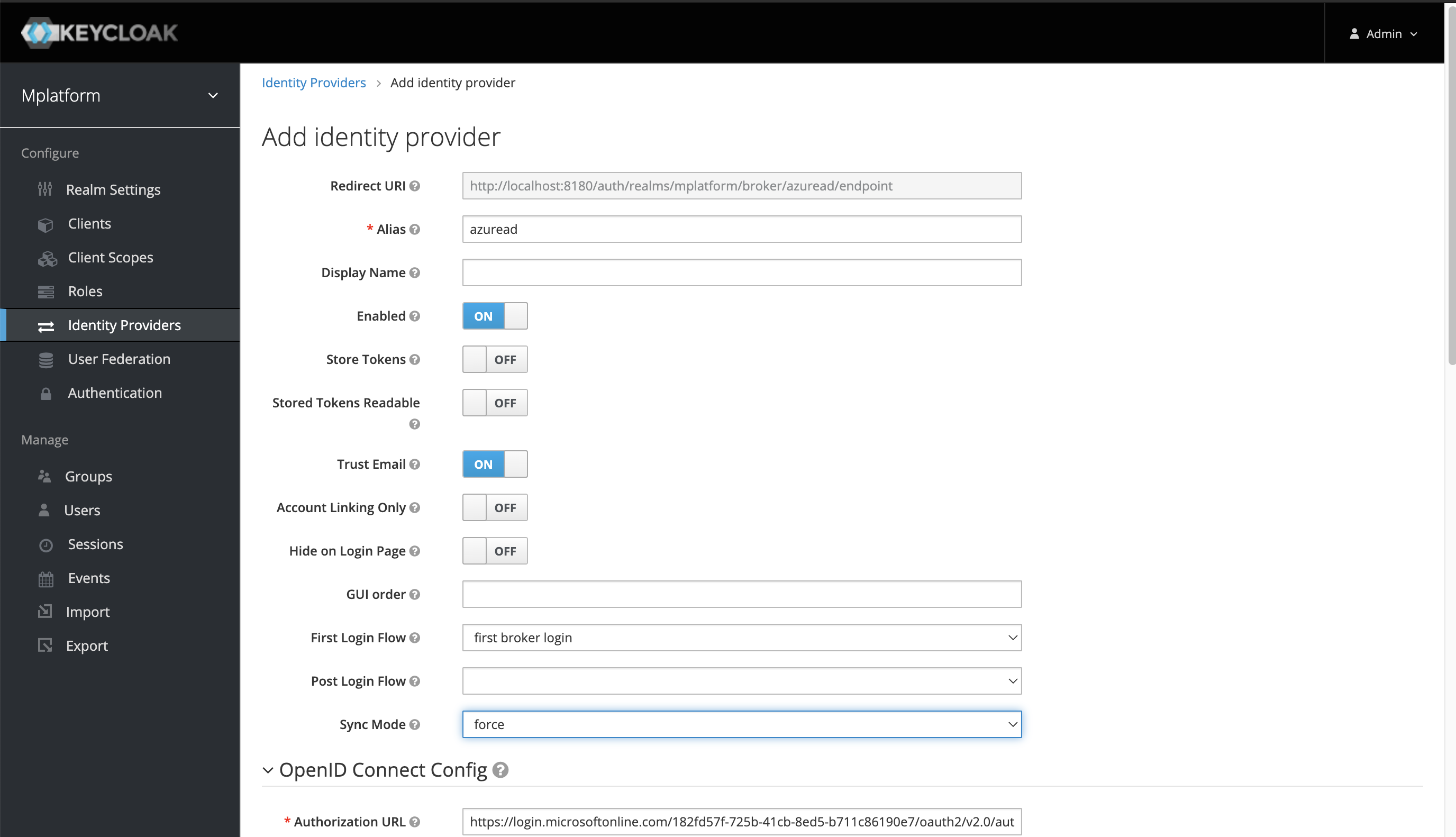

-
-
For the
ClientID, enter the Azure App’sApplicationID. -
For the
ClientSecret, enter Azure App’sSecret Value.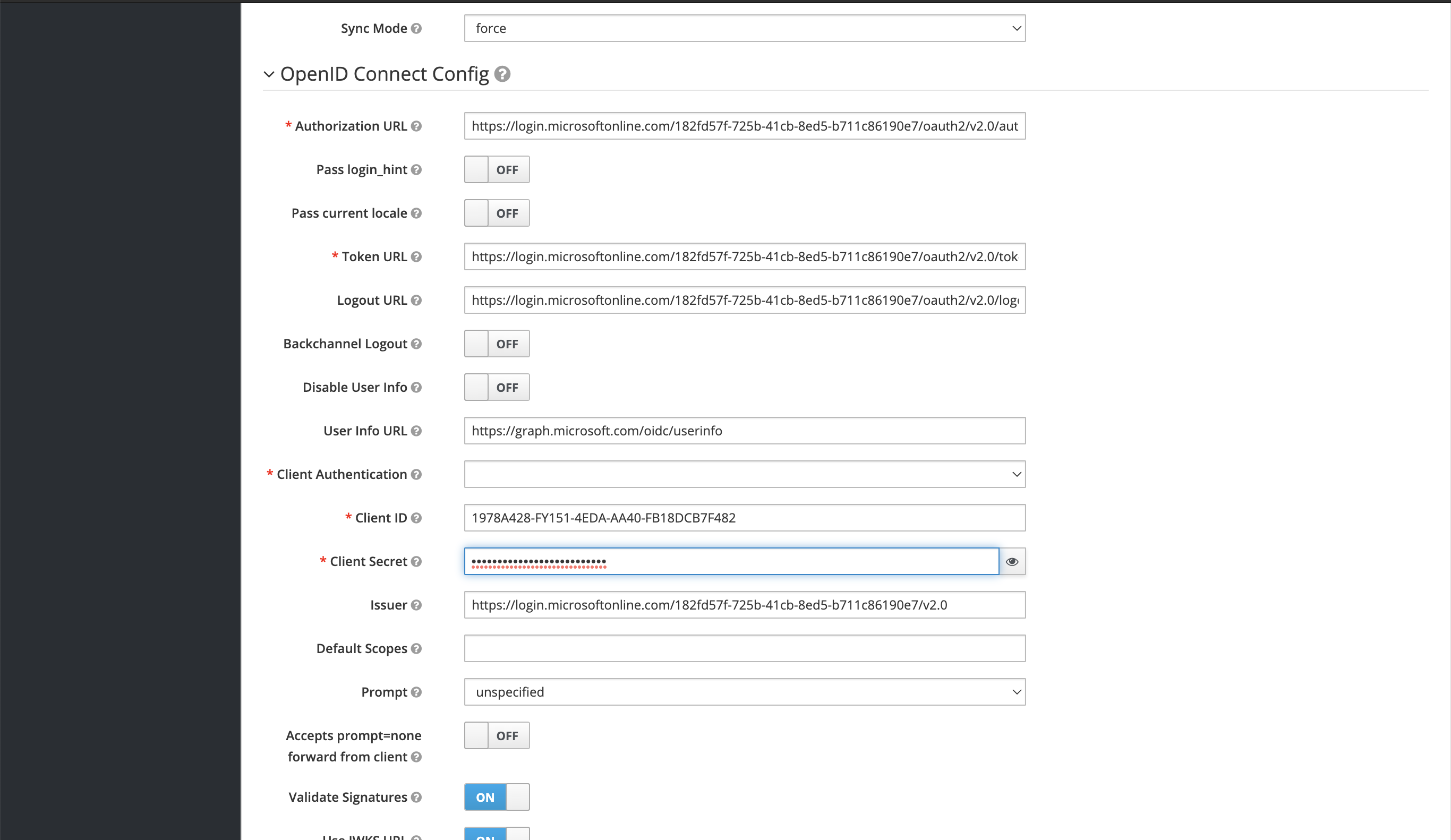
-
Perform a basic Test on Realm ID.
See the URL format https://id.eu-central.magnolia-platform.com/realms/<customer>/account/#/. -
Prepare
RoleMapping(Map OpenID "roles" to existing keycloak roles).
App mapping
IdP naming and structure for groups/users/roles/assignments are flexibe, so it’s important for SSO to align and match on certain role assignments to control granular access privileges.
Aligning Claim-Value with the Role or Group name in both Keycloak and Azure AD helps to avoid any confusion or misconfiguration.
Ensure that these roles are delivered as part of the roles claim in the OIDC Token.
See Microsoft’s App roles vs groups for more information.
|
The following default values can be used as example to prepare an IdP for onboarding with DX Cloud Keycloak.
| Claim-Value/Role | Type | Description |
|---|---|---|
|
Rancher |
Rancher Project Access (all Clusters) |
|
DX Cloud Cockpit |
Cockpit Admin Access (all functions) |
|
DX Cloud Cockpit |
Cockpit DevOps Access (Interact Magnolia Workload, Configuration, Certificates, Redirects, …) |
|
DX Cloud Cockpit |
Cockpit Business Access (Manage commercial aspects, Billing, …) |
|
DX Cloud Cockpit |
Cockpit Support Access (ReadOnly on Logs/Metrics and Support Functions) |
|
DX Cloud Cockpit |
Cockpit User-Management Access (Manage User Roles/Permissions, Enable/Disable Users, …) |
|
Magnolia Admincentral SSO |
Magnolia Author Superuser Access |
|
Magnolia Publisher SSO |
Magnolia Author Publisher Access |
|
… |
… |
-
In App Registrations of your app, create your desired
AppRole(ie. Magnolia, Cockpit, Rancher) to be delivered as an OIDC Claim Value (Value=Claim Valuein Keycloak).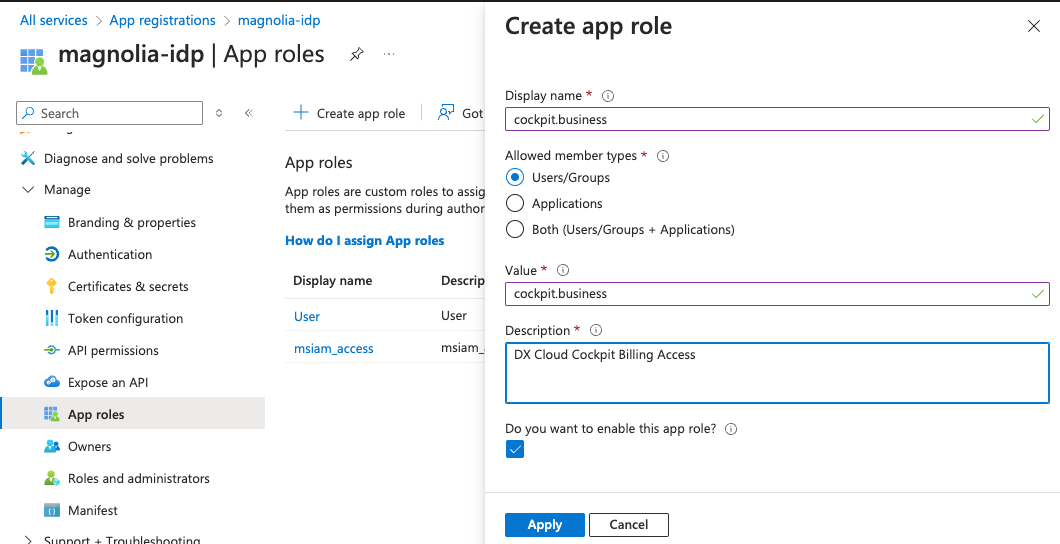
-
In (Enterprise) Application, map the
AppRoleon a User and/or Group Level in Azure AD.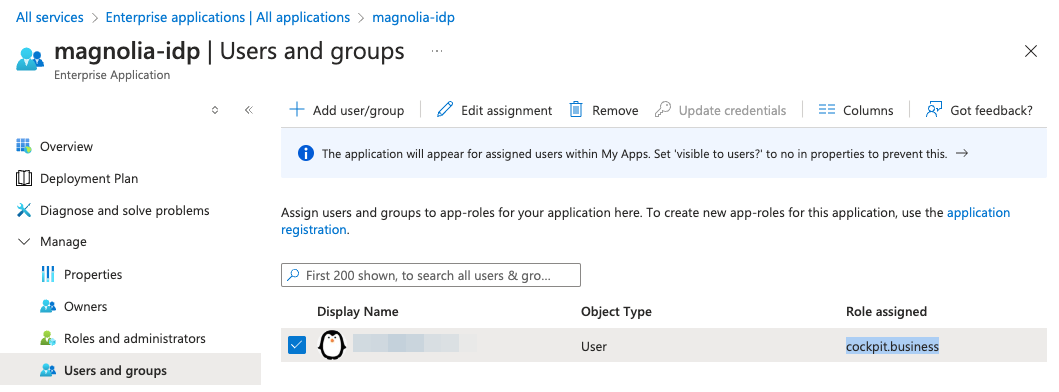 Important if using SSO module
Important if using SSO moduleIf you connect the SSO module to our Keycloak IDP, you must get the
rolesby settingtargetProperty: <value>tomagnolia-roles.authorizationGenerators: - name: groupsAuthorization groups: targetProperty: magnolia-roles (1) ...1 targetPropertymaps to the groups in your IDP for the SSO module. See SSO module: Configuring via yaml for more details.
-
In <customer> > Identity Providers > Mappers, map
Claim Value(set before in Azure asAppRole) of the OIDC Token Claimrolesto the existingRolein Keycloak IdP.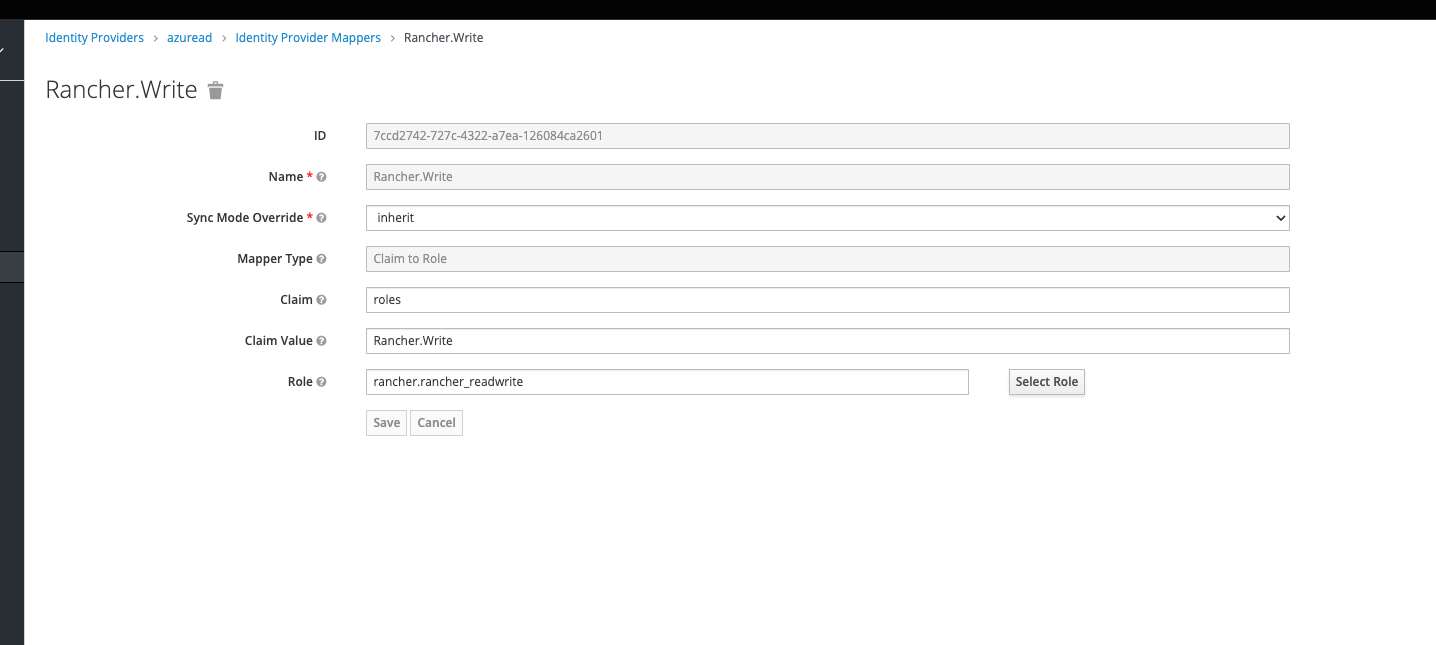
Repeat the steps of App mapping per Application you want to integrate. For more information on installing and configuring the SSO Module and securing Magnolia Admincentral Access, check out SSO module.
Set sameSiteCookies to lax
In your Tomcat configuration, make sure that the CookieProcessor component does not have the sameSiteCookies property set to strict.
Instead, set the property to Lax:
<CookieProcessor sameSiteCookies="Lax" /> (1)| 1 | sameSiteCookies set to Lax instead of strict. |
If the CookieProcessor with sameSiteCookies set to strict, you will likely encounter issues while trying to log into Magnolia.
If you decide to continue using the SSO Module, you need to know that setting this cookie to Lax has the potential to impact site security.
|